Last updated at Thu, 03 Dec 2020 19:23:53 GMT
The ability to detect Dynamic Host Configuration Protocol (DHCP) servers is a feature that has been in network traffic analysis (NTA) tools for some time, but more people are looking for alerts if a rogue DHCP server appears on the network.
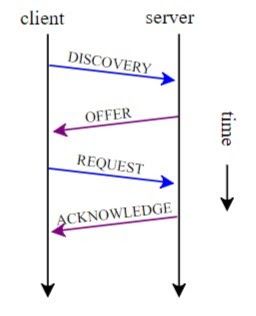
DHCP is a standard internet protocol that enables the dynamic configuration of hosts on an Internet Protocol (IP) internetwork. DHCP is an extension of the bootstrap protocol (BOOTP). The image on the right depicts the breakdown of a typical DHCP client request.
A DHCP server is a machine that runs a service that can lease out IP addresses and other TCP/IP information to any client that requests it. They are usually managed and controlled by the network administrators.
Rogue DHCP servers and their risks
A rogue DHCP server can be defined as one that is not managed by IT. It could be a wireless router added to the network by a user, or someone enabling DHCP services on a server.
As clients connect to the network, both the rogue and legal DHCP server will offer them IP addresses, as well as a default gateway, DNS servers, WINS servers, and others. If the information provided by the rogue DHCP differs from the real one, then clients accepting IP addresses from it may experience network access problems, as well as an inability to reach other hosts because of an incorrect IP network or gateway. IP conflicts can cause problems for existing clients, and they may also experience network access problems.
In addition, if a rogue DHCP is set to provide as a default gateway, such as an IP address of a machine controlled by a misbehaving user, it can sniff all the traffic sent by the clients to other networks. This is typically referred to as a man-in-the-middle (MitM) attack.
Finding DHCP servers
One of the easiest ways to find DHCP servers on your network is to monitor network traffic via a SPAN, mirror port, or TAP. Once you have your packet data source, watch out for DHCP offer packets. These are sent by DHCP servers when a client sends out a broadcast packet looking to discover a DHCP server.
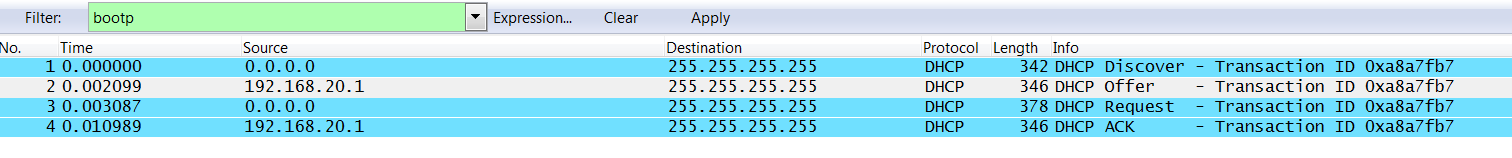
The image below shows the output of a DHCP request sequence as captured by Wireshark. You can use the bootp filter to exclude other packets from the display. This approach is particularly useful for smaller networks where the traffic volumes are low. For larger networks, you may want to consider a tool that includes network traffic analysis (NTA).
Generating alerts if rogue DHCP servers are found
While running DHCP server reports are useful, most of us do not have the time to do this on a regular basis. A tool with a built-in alerting engine can help. For example, let’s say I want to generate an alert if a DHCP server is detected within my 192.168.0.0/24 network range. The steps involved to get this alert setup are:
- Log onto your tool’s interface and find Settings (or the system equivalent)
- Find alert rules
- Click to add a new rule.
- Assign a name to the rule, like ‘Rogue DHCP Servers’
- Select the DHCP module from the dropdown
- Enter the text server_ip=192.168.0.0/24 && message_type=2 as the rule and then save.
You may need to change the IP range to match your own network IP ranges.
To learn more about how to monitor and analyze traffic on your network, check out this short demo of the network traffic analysis features in InsightIDR.
